- 2024.05.19.화.보안 day332024년 05월 21일 10시 25분 16초에 업로드 된 글입니다.작성자: 202401to07
Wayback Machine
We will keep fighting for all libraries - stand with us!
web.archive.org
URL Decode and Encode - Online
Decode from URL-encoded format or encode into it with various advanced options. Our site has an easy to use online tool to convert your data.
www.urldecoder.org
기본설정
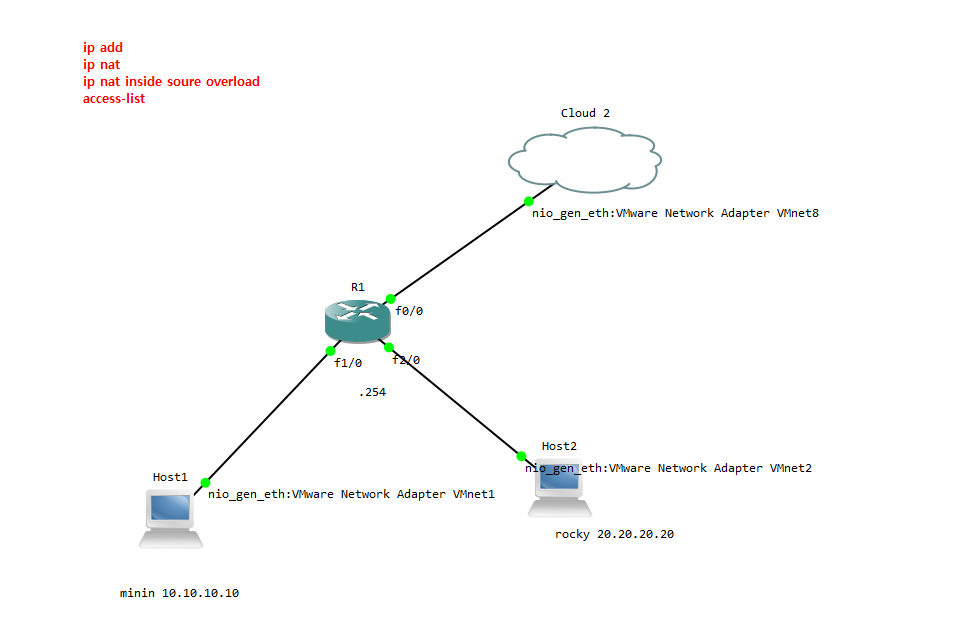
mini) 10.10.10.10 putty 에서
yum install bind* -y
vi /etc/named.conf
//
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
// See the BIND Administrator's Reference Manual (ARM) for details about the
// configuration located in /usr/share/doc/bind-{version}/Bv9ARM.html
options {
# listen-on port 53 { 127.0.0.1; }; 이거 주석으로 바꾸고 any
listen-on port 53 { any; };
listen-on-v6 port 53 { ::1; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
recursing-file "/var/named/data/named.recursing";
secroots-file "/var/named/data/named.secroots";
# allow-query { localhost; }; 이거 주석으로 바꾸고 any
allow-query { any; };
/*
- If you are building an AUTHORITATIVE DNS server, do NOT enable recursion.
- If you are building a RECURSIVE (caching) DNS server, you need to enable
recursion.
- If your recursive DNS server has a public IP address, you MUST enable access
control to limit queries to your legitimate users. Failing to do so will
cause your server to become part of large scale DNS amplification
attacks. Implementing BCP38 within your network would greatly
reduce such attack surface
*/
recursion yes;
# dnssec-enable yes; 이거 주석으로 바꾸고 no
# dnssec-validation yes; 이거 주석으로 바꾸고 no
dnssec-enable no;
dnssec-validation no;
/* Path to ISC DLV key */
bindkeys-file "/etc/named.root.key";
managed-keys-directory "/var/named/dynamic";
pid-file "/run/named/named.pid";
session-keyfile "/run/named/session.key";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones";
include "/etc/named.root.key";vi /etc/named.rfc1912.zones
zone "sevas10.com" IN {
type master;
file "sevas10.zone";
allow-update { none; };
};
zone "korea10.com" IN {
type master;
file "korea10.zone";
allow-update { none; };
};추가
cd /var/named/
cp named.localhost sevas10.zone
vi sevas10.zone[root@localhost named]# cat sevas10.zone
$TTL 1D
@ IN SOA ns.sevas10.com. root.sevas10.com. (
0 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
IN NS ns.sevas10.com.
IN A 10.10.10.10
ns IN A 10.10.10.10
www IN A 10.10.10.10
ftp IN A 30.30.30.30
db IN A 20.20.20.20cp -a sevas10.zone korea10.zone
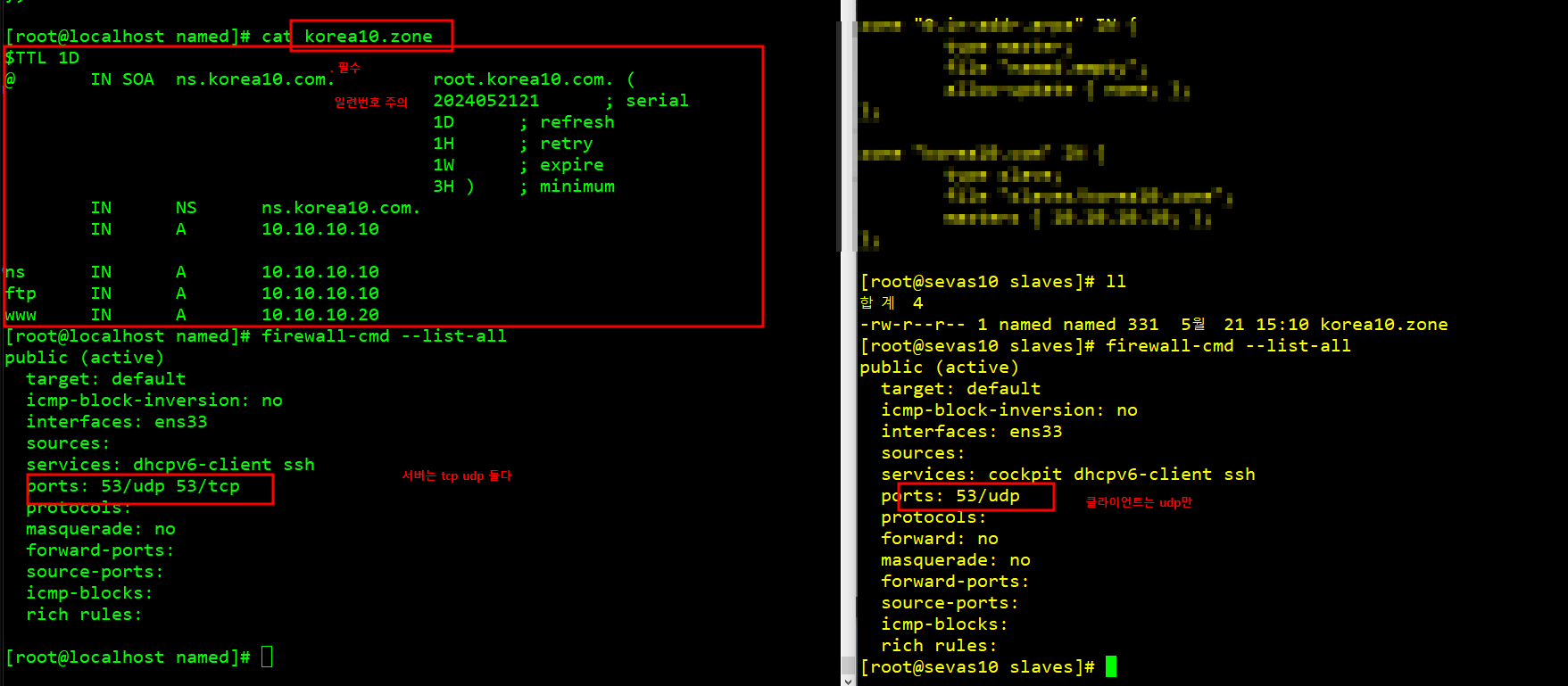
[root@localhost named]# cat korea10.zone
$TTL 1D
@ IN SOA ns.korea10.com. root.korea10.com. (
0 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
IN NS ns.korea10.com.
IN A 10.10.10.10
ns IN A 10.10.10.10
ftp IN A 10.10.10.10cat /var/log/messages : 오류나면 확인
service named restart
chown .named *10.zone
chmod 660 *10.zone오류 있을때
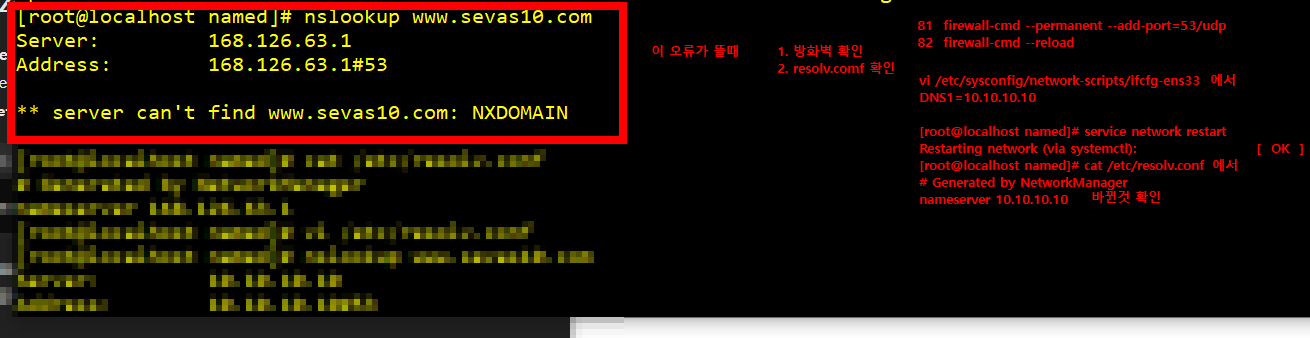
1. 방화벽
2. resolv.conf에서 nameserver가 10.10.10.10이도록
3. vi /etc/sysconfig/network-sc/ifcfg-ens33에서 DNS도 10.10.10.10
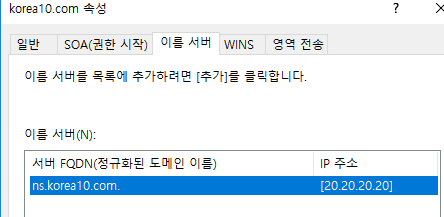
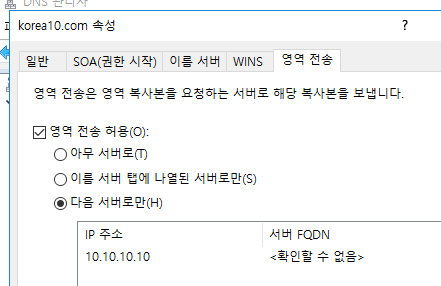
master slave
korea10.zone 파일 받기

최종실습38 yum install bind-* -y
39 vi /etc/named.conf
40 vi /etc/named.rfc1912.zones
41 cd /var/named/
42 ll
43 cp named.empty sevas10.zone
44 vi sevas10.zone
45 ll
46 chown .named sevas10.zone
47 chmod 660 sevas10.zone
48 ll
49 service named restart
50 vi /etc/sysconfig/network-scripts/ifcfg-ens33
51 service named restart
52 service network restart
53 ll
54 nslookup http://www.sevas10.com
55 nslookup http://www.korea10.com
56 vi /etc/named.rfc1912.zones
57 ll
58 cd slaves/
59 ll
60 service named restart
61 ll
62 firewall-cmd --permanent-add-port 53/udp
63 firewall-cmd --permanent --add-port 53/udp
64 firewall-cmd --permanent --add-port 53/tcp
65 firewall-cmd --reload
66 firewall-cmd --list-all
67 service named restart
68 ll
69 vi /etc/named.conf
70 vi /etc/named.rfc1912.zones
71 service named restart
72 ll
73 vi /etc/resolv.conf
74 vi /etc/sysconfig/network-scripts/ifcfg-
75 vi /etc/sysconfig/network-scripts/ifcfg-ens33
76 service named restart
77 ll
78 service named restart
79 l;l
80 ll
81 nslookup http://www.korea10.com
82 vi /etc/named.rfc1912.zones
83 service named restart
84 vi /etc/named.rfc1912.zones
85 vi sevas10.zone
86 ll
87 cd ..
88 ll
89 vi sevas10.zone
90 service named restart
91 vi sevas10.zone
92 service named restart
93 nslookup db2.korea10.com
[root@localhost named]# cat sevas10.zone
$TTL 3H
@ IN SOA ns.sevas10.com. root.sevas10.com. (
1 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
IN NS ns.sevas10.com.
IN A 10.10.10.10
ns IN A 10.10.10.10
www IN A 10.10.10.100
ftp IN A 1.1.1.1
www2 IN A 2.2.2.2
[root@localhost named]# cat /etc/named.conf
//
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
// See the BIND Administrator's Reference Manual (ARM) for details about the
// configuration located in /usr/share/doc/bind-{version}/Bv9ARM.html
options {
# listen-on port 53 { 127.0.0.1; };
listen-on port 53 { any; };
listen-on-v6 port 53 { ::1; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
recursing-file "/var/named/data/named.recursing";
secroots-file "/var/named/data/named.secroots";
# allow-query { localhost; };
allow-query { any; };
/*
- If you are building an AUTHORITATIVE DNS server, do NOT enable recursion.
- If you are building a RECURSIVE (caching) DNS server, you need to enable
recursion.
- If your recursive DNS server has a public IP address, you MUST enable access
control to limit queries to your legitimate users. Failing to do so will
cause your server to become part of large scale DNS amplification
attacks. Implementing BCP38 within your network would greatly
reduce such attack surface
*/
recursion yes;
# dnssec-enable yes;
# dnssec-validation yes;
dnssec-enable no;
dnssec-validation no;
/* Path to ISC DLV key */
bindkeys-file "/etc/named.root.key";
managed-keys-directory "/var/named/dynamic";
pid-file "/run/named/named.pid";
session-keyfile "/run/named/session.key";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones";
include "/etc/named.root.key";
[root@localhost named]# cat /etc/named.rfc1912.zones
// named.rfc1912.zones:
//
// Provided by Red Hat caching-nameserver package
//
// ISC BIND named zone configuration for zones recommended by
// RFC 1912 section 4.1 : localhost TLDs and address zones
// and http://www.ietf.org/internet-drafts/draft-ietf-dnsop-default-local-zones-02.txt
// (c)2007 R W Franks
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
zone "localhost.localdomain" IN {
type master;
file "named.localhost";
allow-update { none; };
};
zone "localhost" IN {
type master;
file "named.localhost";
allow-update { none; };
};
zone "1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa" IN {
type master;
file "named.loopback";
allow-update { none; };
};
zone "1.0.0.127.in-addr.arpa" IN {
type master;
file "named.loopback";
allow-update { none; };
};
zone "0.in-addr.arpa" IN {
type master;
file "named.empty";
allow-update { none; };
};
zone "sevas10.com" IN {
type master;
file "sevas10.zone";
allow-update { none; };
allow-transfer { 20.20.20.20; };
also-notify { 20.20.20.20; };
};
zone "korea10.com" IN {
type slave;
file "slaves/korea10.zone";
masters { 20.20.20.20; };
};

'보안' 카테고리의 다른 글
2024.05.21.목.보안 day35 (0) 2024.05.23 2024.05.20.수.보안 day34 (0) 2024.05.22 2024.05.17.금.보안 day31 (0) 2024.05.17 2024.05.16.목.보안 day30 (0) 2024.05.16 2024.05.14.화.보안 day29 (0) 2024.05.14 다음글이 없습니다.이전글이 없습니다.댓글